Tor is an abbreviation for “The Onion Router.” It is frequently portrayed poorly by the media and law enforcement, although it has numerous advantages. Journalists and sources rely on it to communicate safely and anonymously, free of government intrusion. Secure communication is critical in circumstances of whistleblowing, such as the Edward Snowden revelations. Tor is also useful for law enforcement because it allows for clandestine operations and investigations to be conducted online. Tor presently has over two million daily users globally, with the majority of them coming from the United States, Germany, and Russia.
Tor, like a VPN, may disguise your IP address and anonymize your internet traffic. You can also use the Tor Browser to browse the dark web and run a “hidden service” anonymously. In general, the Tor Browser will not anonymize all of your web traffic, which is why it is frequently used in conjunction with a VPN.
Connecting to Tor using a VPN connection is an excellent approach to protect your internet privacy and security. It will not only conceal your browsing data from your VPN provider, but it will also conceal your home IP address from the Tor entry node.
How the Tor browser works
Assume computers and the internet do not exist, and people continue to communicate by what we now refer to as “conventional mail.”
Assume you wish to buy a book. How did you do that without leaving your house? You may seek up a publishing house’s address in the yellow pages and send them a postcard.
You might express your desire to purchase a book you enjoy on that card, and you could give your own address so the publisher knows where to send it.
Everyone along the delivery route can see what everyone wants to read, which is a problem. They can copy everything or simply keep track of who requested what.
Envelopes keep the contents safe
Requests could be put inside sealed envelopes for further security. Because these cryptographic seals are impossible to crack without breaking them, the post office could only keep track of what was delivered where without knowing what was inside the envelopes.
The metadata refers to information such as the size and weight of the envelope, as well as the sender and recipient’s names.
Metadata shows a great deal. For example, just by looking at the envelope, you may know if you’ve received a speeding ticket. The mailman can, too.
This is quite similar to how the internet operates now. Cryptographic seals take things a step further by being difficult to crack. Basic encryption, such as Transport Layer Security (TLS), has become a web standard in recent years. (When this is enabled, a lock icon will appear in your address bar.)
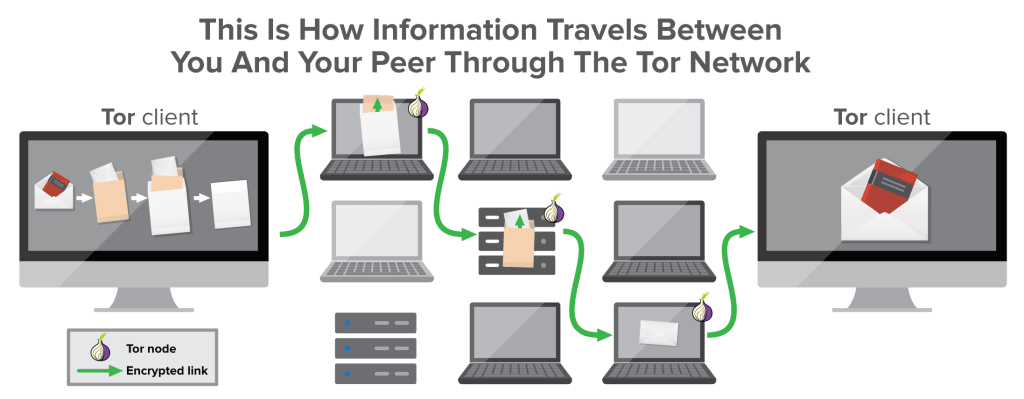
Tor circuits are based on a network of nodes
To transmit requests anonymously in the Tor network, first, create a Tor circuit. You accomplish this by sending your “sealed postcard” to a random Tor node. This address could be either residential or commercial. It could be your neighbor’s house or a large structure in another nation. This is your entry node, and all of your sealed mail will be delivered to it. This address will also be used for all future correspondence.
Your message will be forwarded by your entry node to another node, which will then forward it to another node—the exit node. The address of the intended recipient is only known to the exit node.
Tor is run entirely by volunteers
Tor might theoretically operate with physical mail, but the effort required to redirect mail and seal envelopes would be enormous. Although the Tor principle is significantly easier to implement electronically, the network continues to rely on volunteers who install Tor nodes on their servers or at home.
The exit node is the weakest link in this chain. There is no guarantee that the exit node is not logging the contents of your requests, modifying them, or injecting malware into them if the connection to the website you are visiting does not use TLS encryption. If your system is not properly configured, cookies or the contents of your messages could still be used to identify you.
To circumvent exit nodes on the dark web, use .onion addresses
There is a way to avoid utilizing exit nodes entirely. However, in order for this to work, the website you are browsing must have a .onion address. This address is not the same as a standard domain name because it cannot be properly registered. Domain names are typically alphanumeric strings produced by a public cryptographic key. Using such a domain not only removes the exit node from the equation but also prevents both the user and the site from knowing where the other party is.
Many well-known websites have .onion domains: ExpressVPN’s is http://expressobutiolem.onion/, whereas Facebook’s is facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion. (Please keep in mind that you will require the Tor Browser to view this and other .onion sites.)
Facebook is also one of the few sites that have TLS certificates for their .onion domains. This does not greatly increase the privacy or security of the content, but it can aid in determining whether the site you are connected to is the one you intended to visit. Many sites are only accessible via their .onion address in order to remain uncensorable and to conceal their location. This area of the Internet is commonly referred to as the dark web (not to be confused with the deep web).
In practice,.onion addresses have an additional purpose. They are a simple solution for making your devices accessible within restricted networks with stringent firewalls, such as student residences or corporate complexes. If you wish to host a personal server in such an environment, for example, utilizing tor and an onion address is a straightforward approach to make this device reachable from the outside.