Well, it seems hackers are up to their old tricks again, targeting Linux servers with weak security to try and spread their malware far and wide.
According to researchers at AhnLab Security, these cybercrooks are launching brute force dictionary attacks on SSH logins, trying countless username and password combos until they luck their way in. Once inside, they start installing all kinds of tools to scan for more servers to infect or sell off access to the highest dark web bidder.
The researchers spotted baddies uploading port scanners to poke around for other machines with port 22 open. That particular port is a sign that more SSH services are running and vulnerable. From there, the options are practically endless for profit and digital mayhem.
Sometimes the hackers will straight up install cryptocurrency miners or DDoS botnets to overwhelm websites with junk traffic. Other times they’ll offer up login credentials and access on hacker forums to spread their work around.
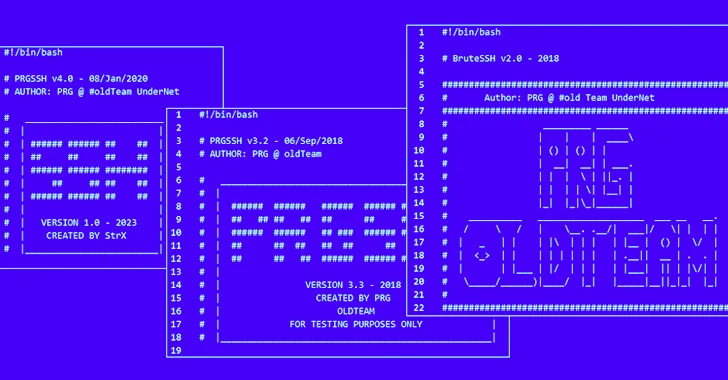
“Threat actors can also choose to install only scanners and sell the breached IP and account credentials on the dark web,” said the researchers. “These tools are believed to have been created by PRG old Team, and each threat actor modifies them slightly before using them in attacks.”
So what’s the best way to lock these baddies out? Strong passwords, my friend – the longer, more complex and downright nonsensical, the better. Using a mix of upper and lower case letters, numbers and symbols is a must. Anything that looks like an actual word or ties to personal info is prime fodder for dictionary attacks. A little password security goes a long way to protect servers!